If you’ve been following the Configuring Single Sign-On with SAML 2.0 on the WSO2 Identity Server Documentation, but can’t seem to figure out how SSO works on it, you’ve arrived at the right place. In this post I’ll be explaining my understanding of how the sample works. This might not be the most accurate description, so please feel free to drop a comment if I’ve mistaken something :)
You can checkout the sample from the SVN repository using the command given below.
The tree structure is given below,


Here the most important files for the purposes of this tutorial are, the java classes, the properties files, the web.xml and the home and index java servlet pages. The rest can be disregarded since they are not concerned with SSO.
To make this tutorial simple, we’ll be going through each of the components similar to the order in which they are referred in SAML2 based SSO. So once you have done the configuration based on the tutorial and the war file is deployed on tomcat, the first thing that happens when you visit http://localhost:8080/travelocity.com is that you will be directed to the index page.
Part 1: The index.jsp
Given below is the index page of the travelocity sample.

For this tutorial, we shall only be focused on “login with SAML from WSO2 Identity Server”. If you look at the source code of the index.jsp page, you will see that the hyperlink for the SAML Login is “samlsso”
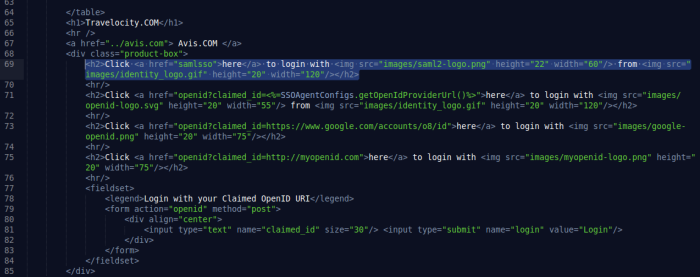
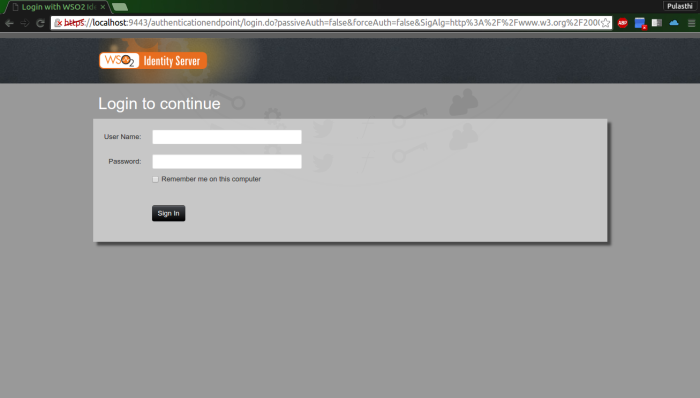
So when you click on the “here” hyperlink, you will get redirected to http://localhost:8080/travelocity.com/samlsso but in reality you get directed to the authentication page of the WSO2 Identity Server which is given below.
This is where the next component comes into play. So let’s look at the SSOFilter.
Part 2: The SSOFilter
A filter is a way of performing filtered functionality on a java web application. Typically filters are used to perform some piece of functionality either before or after the primary functionality of the web application. The architecture of the filter is given below.
How the filter is triggered will be discussed in the web.xml (Part 3).
In this scenario, the SSO functionality has been implemented in the form of a filter using the WSO2 library org.wso2.carbon.identity.sso.agent. When the filter is triggered, the request is sent through the SSOFilter. Here a SAML Assertion is generated and the browser is redirected to the WSO2 IS authentication page and once a user is authenticated, the SAML Response is again sent through the filter. During this process the SAML response is validated using the public and private key pair found in the wso2carbon.jks file. Once the user is validated, the browser is redirected to the home.jsp which is the Assertion Consumer URL.
Part 3: The web.xml
The web.xml is the deployment descriptor file of a java web application and is used to determine how URLs map to servlets, which URLs require authentication, and other information. It can be found inside the WEB-INF directory in the webapp folder.
In the web.xml of travelocity, the SSOFilter is defined.
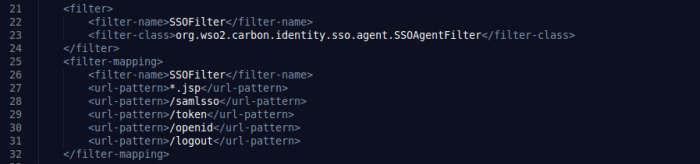
Here the filter class name is given to locate the jar file from the libraries. The jar file was added as a dependency in the pom.xml.
The filter mapping is used to initialize the filter. When a particular url is requested, if it contains any of the url-patterns as given in the filter mapping, the particular filter is initiated. In this scenario, when the url http://localhost:8080/travelocity.com/samlsso is requested, since it contains the /samlsso url pattern, the SSOFilter is initiated.
Now once the request is sent through the SSOFilter and the SAML Response is validated, the user is then redirected to the Assertion Consumer URL. In this case the consumer url is http://localhost:8080/travelocity.com/home.jsp. So next let’s look at the home.jsp.
Part 4: The home.jsp

In this example, the default dashboard of the webapp is implemented within the consumer url itself, but in practical situations, the consumer url merely redirects the user to the particular dashboard of the logged in user.
Given below is the source of the home.jsp.
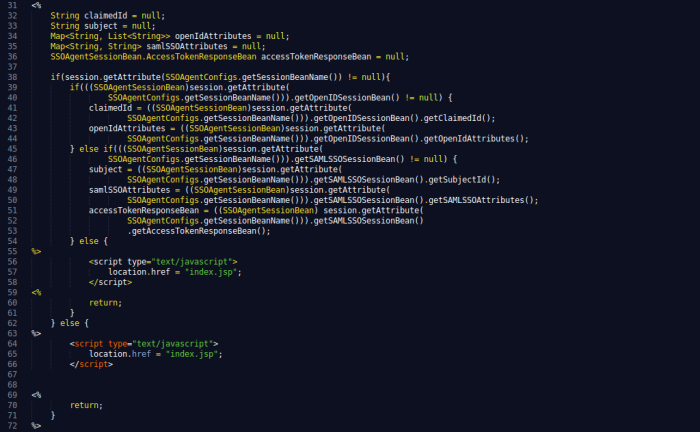
The first few lines of code in the home.jsp are there to retrieve the attributes from the response. the claimedID and openIDAttributes are irrelevant because we are only focused on SAML in this tutorial. The subject is the username of the logged in user. The samlSSOAttributes and accessTokenResponseBean are also saved if needed to be used. At any point if any of the if statements become false, that means that the user is not validated, and redirects the browser back to the index.jsp.
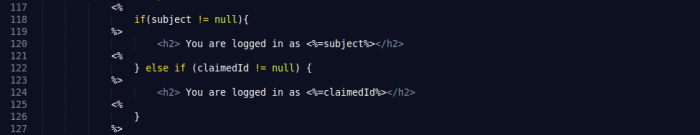
The rest of the home.jsp is HTML and is fairly irrelevant except for the part where it displays the username of the logged in user from the subjectID.
That concludes the SAML process but to fully understand the working of SSO, it’s important to know how the properties file is defined and how it is loaded.
Part 5: The travelocity.properties
The file is found inside the resources folder and this file contains all the information about SAML based SSO for the travelocity.com webapp. The file is loaded to the SSOAgentConfigs by the SampleContextEventListener.java, which will be discussed in the next part.
The information in the properties file such as the issuerID, the Assertion Consumer URL are used by the SSOFilter to identify the Service Provider in the WSO2 Identity Server. This also says if the response and assertion are signed or not, which needs to be configured in the IS.
Other information such as the Keystore Password are used to retrieve the public and private keys from the keystore wso2carbon.jks, to validate the saml response received by the filter.
It is important to understand that the properties file nor the keystore are used by the web application but rather are used by the SSOFilter.
Part 6: The SampleContextEventListener.java
So how does the SSOFilter know where to find the properties file and the keystore. This is where the SampleContextEventListener.java is used. The SampleContextEventListener is initialized as a listener in the web.xml as follows.
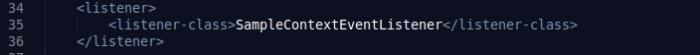
When the webapp is deployed, the SampleContextEventListener loads the properties file and the keystore to the SSOAgentConfigs in the org.wso2.carbon.identity.sso.agent library. From here it is again retrieved whenever needed.
So that’s a brief explanation as to how the travelocity.com sample works, there’s much more to it, specially the functioanlity of the SSOFilter. Hope I covered everything correctly, do drop a comment if I’ve missed anything.